Ransomware is keeping the corporate world on its toes worldwide. The trojans attack entire networks and encrypt all the data they can find. Databases, patient files, CAD drawings - nothing is safe from the sophisticated malware. But how does ransomware actually work? How does it get into the company network and how can you protect yourself against it?
What is ransomware?
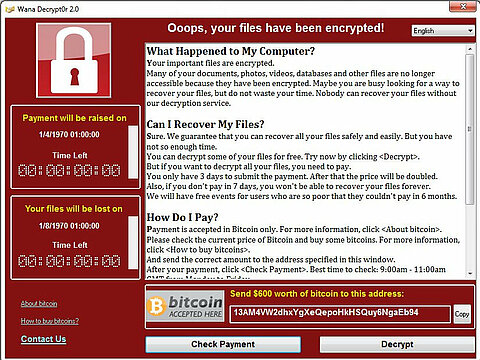
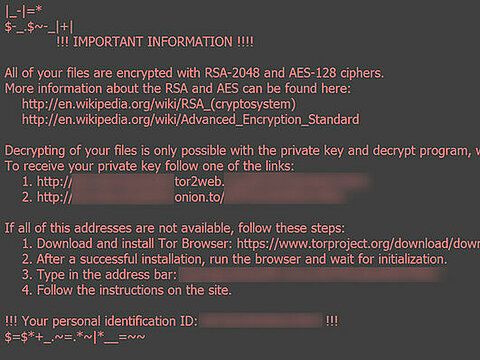
Ransomware is a type of malware that encrypts important files, thus rendering them unusable, and demands payment of a not inconsiderable sum of money for decryption - usually in the form of Bitcoins, where the flow of money is easier to disguise than with conventional currencies. The data is held hostage by the malware and is only released again upon payment of a ransom. Because of the way they work, these malware are therefore often also called "blackmail trojans", "encryption trojans" or "crypto trojans".
Famous examples in the corporate environment
How does ransomware work?
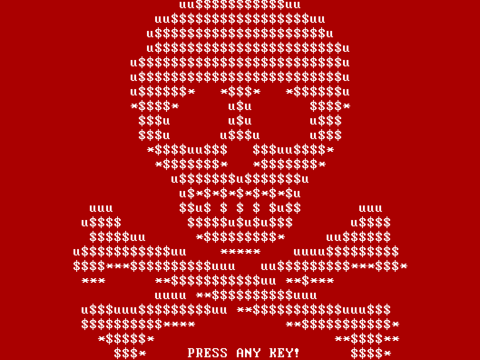
There are currently three main types of ransomware: Screenlockers are a more harmless variant that only lock the user's screen and deny him access to his system. They can be removed relatively easily and do not cause any further damage. File crypters encrypt files on the hard disk so that they cannot be recovered without the appropriate key. The most dangerous type are so-called wipers: Just like file crypters, they encrypt the data on the hard disk and demand a ransom - only here it is not intended that they actually restore the data. Wipers are programmed to delete as much data as possible and thus cause maximum damage - regardless of whether a ransom has been paid or not.
Beware of email attachments
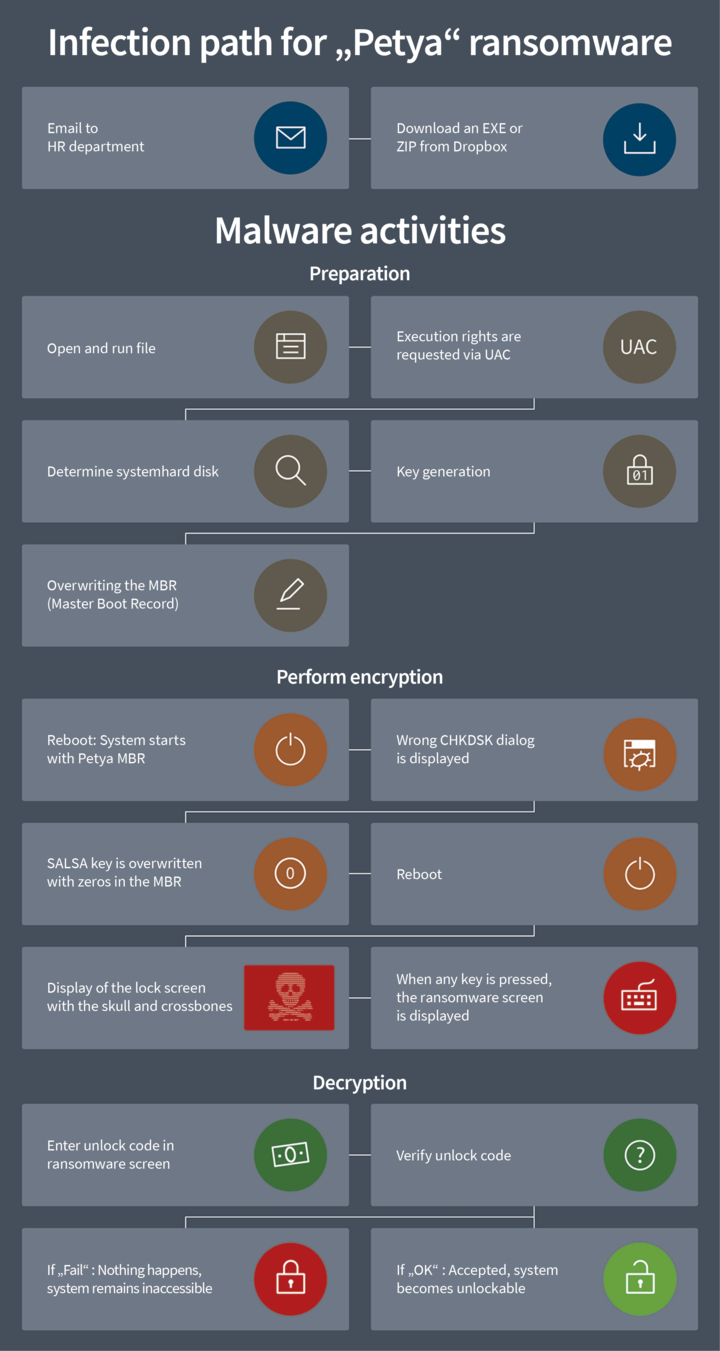
Ransomware usually comes via email: The blackmailers often send emails with a malicious attachment. The malware disguises itself, for example, as an Excel spreadsheet with macros or as an EXE file that looks like a harmless ZIP archive. When the user opens the file, he or she unwittingly installs the trojan. At the latest, the trojan begins to encrypt the files on the computer's hard drive and all connected drives when the computer is rebooted.
Some representatives (such as WannaCry) additionally function like a worm and attempt to infect other computers via the network. It is worth noting that the blackmailers are sometimes very clever: For example, the "GoldenEye" malware, which was rampant in 2016, targeted human resources departments in Germany. The emails were written in impeccable German and referred to actual job advertisements of the company. Even cautious employees in the HR department therefore opened the attached files and thus infected their computers.
The only thing that then appears on the screen of the affected clients is a ransom note promising to decrypt the data again in exchange for payment. To do this, the user is supposed to enter an individual serial number, which he can buy on websites in the Tor network in exchange for Bitcoins. To lend weight to the demand, some files are often deleted every few hours until finally there is no more data left. Usually, the serial number increases in price just as regularly to force the user to act quickly.
How can I protect my business?
Make regular backups
Back up the data of all clients regularly on network drives, external hard drives or in the cloud. Caution: Make sure that the connection to the storage medium or network drive is disconnected after each backup - otherwise there is a risk of all backups being encrypted!
Install updates and patches
Always keep software such as the operating system, browser and plug-ins up to date. Exploiting security gaps in programmes is one of the most popular methods used by cyber criminals. A central patch management helps you to keep the software on all your clients up to date and thus offer malware as little attack surface as possible.
Be wary of e-mails and links
A healthy dose of suspicion does no harm. The email in your inbox is full of typos? Or promises you a lot of money without you having to do anything? You don't know the sender? Delete suspicious e-mails immediately without opening them. Disguised as invoices, application documents or a link to an interesting website, the malware hides in the attachment. Be especially careful with executable EXE files and Office documents that contain macros. It is best to prevent the automatic execution of macros in the Office suites of all clients. Sensitise your employees in seminars to be careful and how they can recognise potentially dangerous files and processes.
G DATA security solutions offer special spam protection with OutbreakShield technology. This protection detects harmful e-mails even before they are loaded onto the computer by the e-mail programme. This means that the email with the harmful content is not delivered in the first place or is removed directly from the mailbox.
Use an up-to-date security solution
Ransomware is a type of malware. Virus scanners and behavioural monitoring detect known ransomware before it can cause damage. Additional protection against exploits can also prevent infection. Often, malware is also detected by universal code sequences typical of compression, encryption, download routines, backdoor activities, cloaking mechanisms or the like. Heuristic and generic signatures recognise such universally valid command sequences even in previously unknown malware families.
However, ransomware does not only spread via email - but also via websites or other Internet services ("drive-by attacks"). G DATA security solutions work with the URL cloud, which keeps a constantly updated list of websites that have been compromised and are now supplying computers with malware unnoticed. If a page has been marked as harmful, access is blocked. In addition, the G DATA software checks all incoming data in the browser for malicious code - be it file downloads or active scripts in the website.
What to do if your network has been infected
If your network is infected by ransomware despite all precautionary measures, you should immediately isolate the affected clients or servers. Cut all network connections (preferably physically) so that the malware cannot spread any further. Then reset the infected computers and restore the last backup. Scan all other clients and servers in the network with a reliable security solution to rule out infection. This step is very important: Some malware hides in the operating system in order to strike at a later point in time - a client that appears "clean" at first glance may well be infected with malware.
If you do not have a current backup of the infected client or server, your data is not necessarily lost: Especially for older ransomware, there is often already an antidote. Experienced security experts have cracked the encryption routines of many pests and developed programmes that can decrypt the data again and render the ransomware harmless. Look on the Internet for corresponding tools, which are usually named "XY Decrypter" or similar.
If the situation is more complex or conventional methods do not help, professional advice from an experienced service provider in the field of IT security is a good idea. The experts at G DATA Advanced Analytics, for example, not only offer first aid for security incidents ("incident response"), but also data recovery measures and in-depth malware analysis. This way, after an infection, you can be sure that the malware does not hide deep in the systems and break out again at a later time.
ransomware victims have paid in the last two years. Ransomware has become a multi-million dollar business for cybercriminals.
Source: Research at Google, July 2017
at most is what the "Cerber" ransomware needs to fully encrypt a computer after infecting it.
Source: Research at Google, July 2017